Network security monitoring with PRTG
Proactively prevent network intrusions and data breaches
- Monitor firewalls, servers, open ports, as well as your entire network
- Scan your network for malicious activity to quickly identify cyberattacks
- Ensure quick incident response with real-time notifications
PRTG network security monitoring: What you’ll find on this page
PRTG makes network security monitoring as easy as it gets
Custom alerts and data visualization let you quickly identify cybersecurity threats and prevent security incidents.
Advantages of using PRTG as your network security monitoring service
As part of your central security plan and security compliance, Paessler PRTG is your reliable addition to standalone network security tools. Our comprehensive network monitoring software adds a double layer of protection by working in real time to quickly identify irregularities and threats and keeping your network secure.
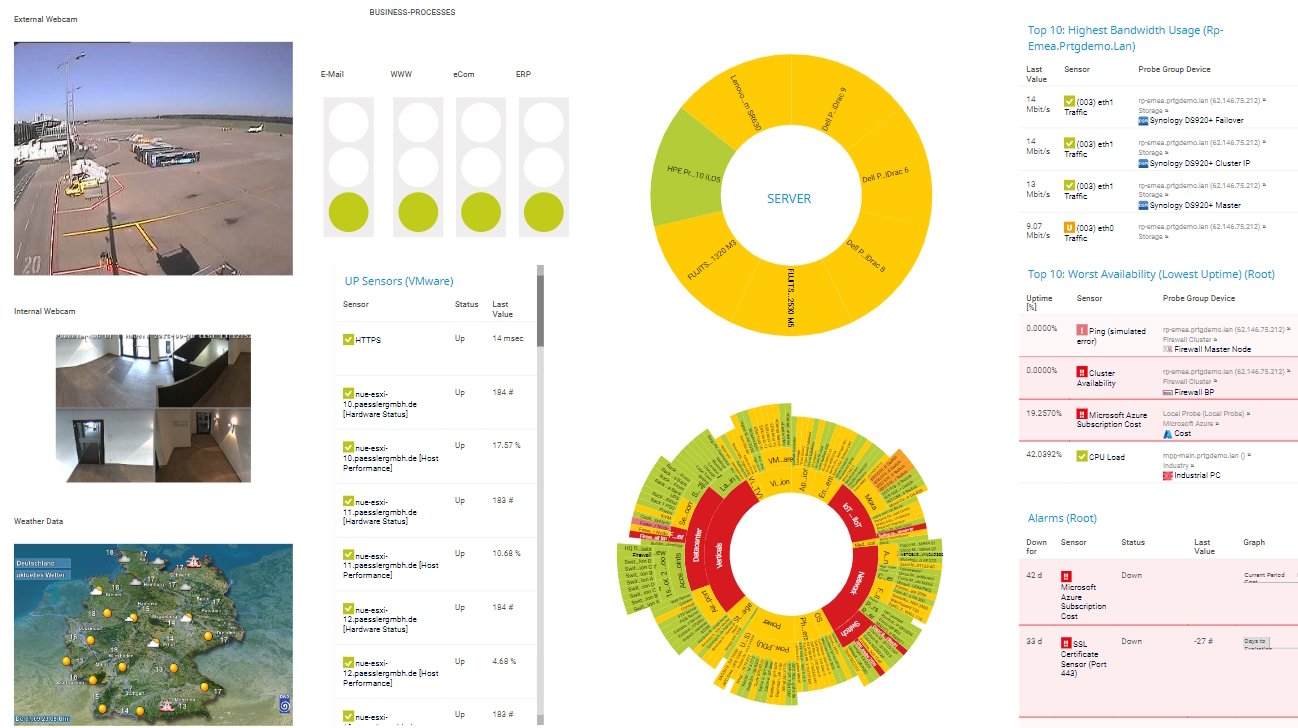
Centralized monitoring
No need to juggle several different monitoring tools at once. The central dashboard of PRTG provides the overview you need – at one glance only.
Keep a constant eye not only on security-relevant network data and devices, but also on other services and processes in your entire IT environment.
Continuous availability
Make sure that the hardware and software that’s important for your network’s security is available and functioning round the clock.
PRTG monitors all your network devices and applications 24/7, including firewalls, ports, routers, switches, VPN connections, antivirus software, and more.
Custom alerts & notifications
The built-in alarm feature of PRTG is fully customizable. Choose your own warning and error threshold values and how you’d like to be informed.
As soon as PRTG detects suspicious activity or unusual traffic patterns on your network, it alerts you via SMS, email, in-app push notification, and other methods.
Historical monitoring data
Every PRTG sensor is equipped with an “unusual” sensor status, and will automatically sound the alarm if values emerge which are inconsistent with previous ones.
Such values may be indicative of security problems – comparing and analyzing them with PRTG’s historical data will help you troubleshoot potential threats and vulnerabilities more efficiently.
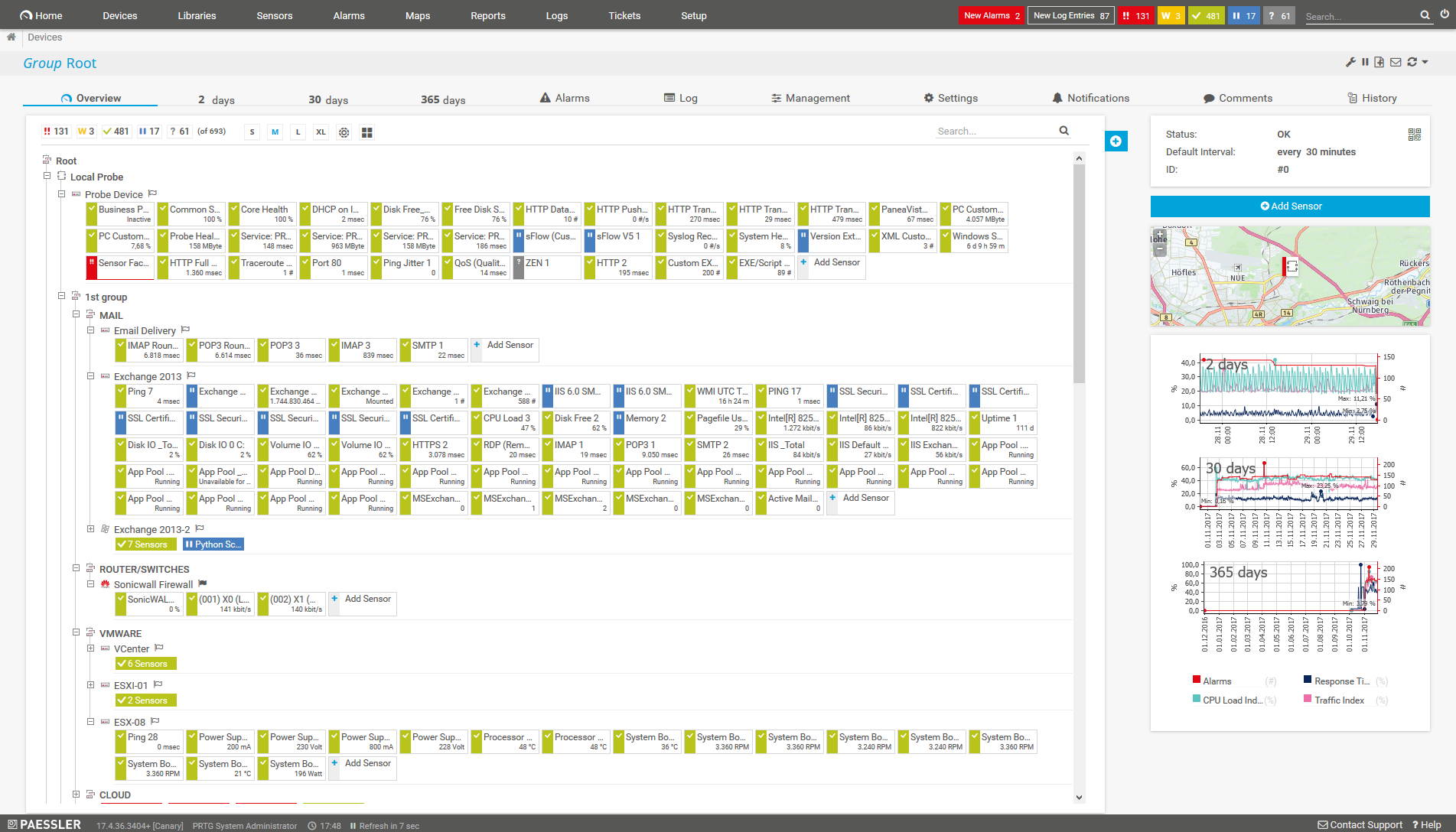
What IT security monitoring looks like in PRTG
Diagnose network issues by continuously tracking the availability and performance of security-relevant hardware and software. Show update status, unusual activities, network traffic flows, bottlenecks, unauthorized access, and other key metrics for threat detection in real time. Visualize monitoring data in clear graphs and dashboards to identify problems more easily. Gain the overview you need to troubleshoot all kinds of cybersecurity issues in your network.
Start monitoring network security with PRTG and see how it can make your network more reliable and your job easier.
5 ways PRTG complements network security systems
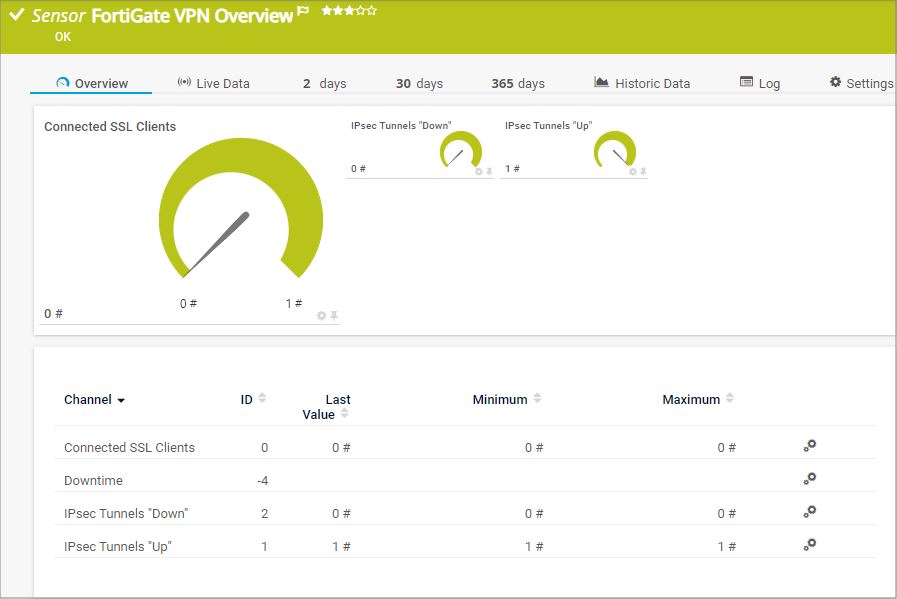
Catch firewall malfunctions
PRTG immediately lets you know if your firewall is not configured properly or is down (which means all gates to your network are open).
Set up preconfigured sensors for monitoring the firewalls of major manufacturers such as Cisco, Juniper, Fortinet, or SonicWall with just a few clicks.
Detect network traffic anomalies
PRTG lets you know if an attack on your IT infrastructure has caused an unusually large amount of traffic flow through your network.
Use the Packet Sniffer sensor or various flow sensors (NetFlow, jFlow, sFlow, IPFIX) to analyze traffic by IP address, port, or network protocol and sound the alarm if something’s not quite right.
Check Windows updates
PRTG helps prevent security loopholes that expose your network to hackers all over the world.
The preconfigured Windows Updates Status (PowerShell) sensor immediately informs you if a new update is necessary, and identifies which network computers are causing vulnerabilities due to unpatched Windows versions.
Look for and close open ports
Open ports are necessary, but can be dangerous and lead to vulnerabilities. It’s no secret that they can be used to illegally access a network or introduce Trojans.
With PRTG’s Port v2 sensor, you’ll always be in the know about which TCP ports are open and which are closed, which will come in handy if you need to open specific ports on a temporary basis.
Keep virus scanners updated
Even the best antivirus scanner software and malware detector is of no use if it is outdated or not available.
The WMI Security Center sensor helps you monitor the status of antivirus software on the clients in your network to prevent network attacks and other cybersecurity issues.
Your network security monitor at a glance – even on the go
Set up PRTG in minutes and use it on almost any mobile device.
Find the root cause of the problem with our PRTG network security monitoring solution
Real-time notifications mean faster troubleshooting so that you can act before more serious issues occur.
PRTG is compatible with all major vendors, products, and systems
Create innovative solutions with Paessler’s partners
Partnering with innovative vendors, Paessler unleashes synergies to create
new and additional benefits for joined customers.
ScriptRunner
With ScriptRunner, Paessler integrates a powerful event automation platform into PRTG Network Monitor.
“Excellent tool for detailed monitoring. Alarms and notifications work greatly. Equipment addition is straight forward and server initial setup is very easy. ...feel safe to purchase it if you intend to monitor a large networking landscape.”
Infrastructure and Operations Engineer in the Communications Industry, firm size 10B - 30B USD
PRTG makes network security monitoring as easy as it gets
Custom alerts and data visualization let you quickly identify cybersecurity threats and prevent security incidents.
PRTG: The multi-tool for sysadmins
Adapt PRTG individually and dynamically to your needs and rely on a strong API:- HTTP API: Access monitoring data and manipulate monitoring objects via HTTP requests
- Custom sensors: Create your own PRTG sensors for customized monitoring
- Custom notifications: Create your own notifications and send action triggers to external systems
- REST Custom sensor: Monitor almost everything that provides data in XML or JSON format
We asked: would you recommend PRTG?
Over 95% of our customers say yes!
Paessler conducted trials in over 600 IT departments worldwide to tune its network monitoring software closer to the needs of sysadmins.
The result of the survey: over 95% of the participants would recommend PRTG – or already have.
Still not convinced?
More than 500,000
sysadmins love PRTG
Paessler PRTG is used by companies of all sizes. Sysadmins love PRTG because it makes their job a whole lot easier.
Monitor your entire IT infrastructure
Bandwidth, servers, virtual environments, websites, VoIP services – PRTG keeps an eye on your entire network.
Try Paessler PRTG
for free
Everyone has different monitoring needs. That’s why we let you try PRTG for free.
Start monitoring network security with PRTG and see how it can make your network more reliable and your job easier.
|
PRTG |
Network Monitoring Software - Version 25.1.104.1961 (April 7th, 2025) |
|
Hosting |
Download for Windows and cloud-based version PRTG Hosted Monitor available |
Languages |
English, German, Spanish, French, Portuguese, Dutch, Russian, Japanese, and Simplified Chinese |
Pricing |
Up to 100 sensors for free (Price List) |
Unified Monitoring |
Network devices, bandwidth, servers, applications, virtual environments, remote systems, IoT, and more |
Supported Vendors & Applications |
|










Combining the broad monitoring feature set of PRTG with IP Fabric’s automated network assurance creates a new level of network visibility and reliability.